Hi folks,
In this article I’ll share the results of ad-hoc security vulnerabilities research I’ve done on windows 8 apps deployment. Specifically, we’ll discuss fundamental design flaws that allow to Reverse Engineer Win8 apps, modification of installed apps and the negative implications on Intellectual Property rights protection, Licensing models and overall PC security. Finally we’ll discuss some creative ideas on how to mitigate these security issues.
Meet the mother-load: C:\Program Files\Applications
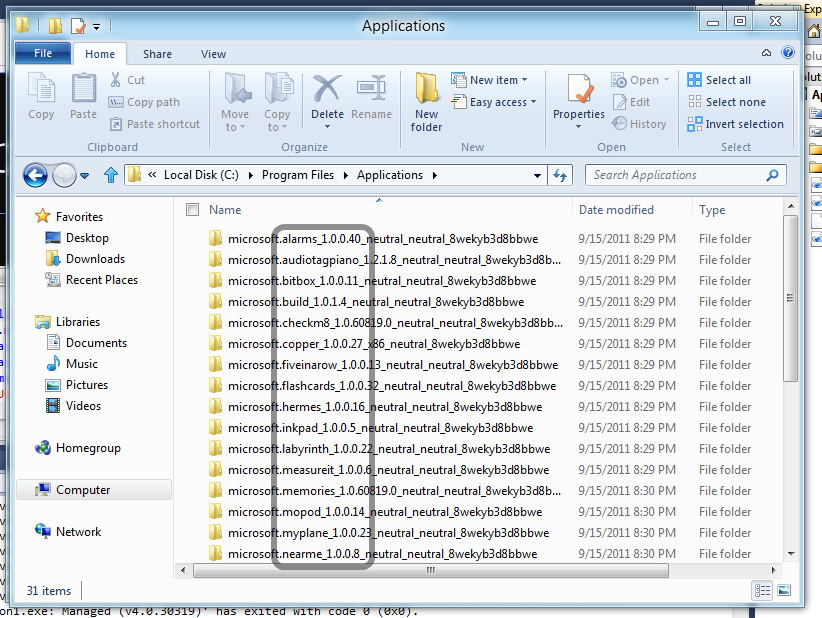
All Windows 8 applications in the developer preview are installed under the clandestine C:\Program Files\Applications location. I will hazard a guess and say that once the Windows App Store goes online it will install all apps under that folder. Currently the folder is an invisible one and cannot be accessed from Windows Explorer user interface on a new Win8 developer preview install.
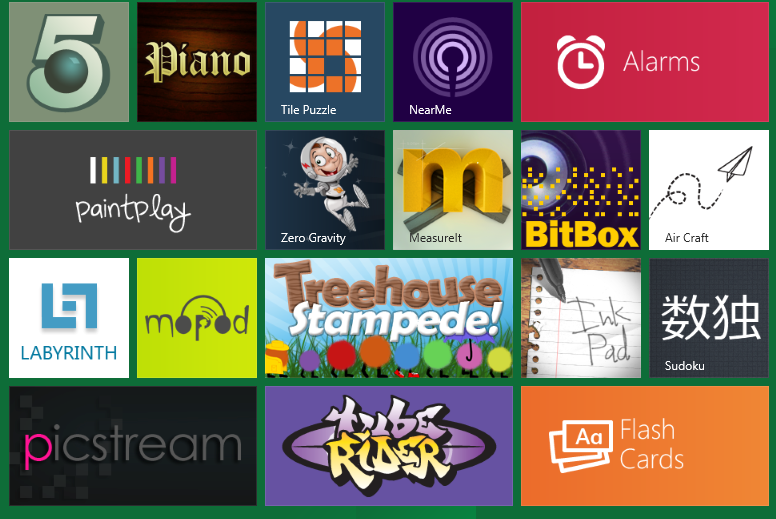
Here’s an example of some of the 29 apps Win8 apps installed on the Win8 developer preview:
And here’s the hidden folder backing it up:
Gaining Access to C:\Program Files\Applications
In essence you’ll need to navigate to that folder, hit “Security Tab” and set yourself up as the owner. Let me walk you through that process step-by-step.
1. Type in “C:\Program Files\Applications” in the Windows Explorer address bar and hit enter.
Read more: Justin Angel
QR: 